Blog / How Help Desk and IT Support Impacts Your Business Efficiency
 Businesses rely heavily on their IT infrastructure to stay competitive. A poorly managed IT environment can cause disruptions, security issues, and even loss of productivity. 94% of businesses report that a single hour of downtime can cost them over $100,000. This statistic shows how crucial it is to have the right IT support. Kelvin […]
May 20, 2025
Businesses rely heavily on their IT infrastructure to stay competitive. A poorly managed IT environment can cause disruptions, security issues, and even loss of productivity. 94% of businesses report that a single hour of downtime can cost them over $100,000. This statistic shows how crucial it is to have the right IT support. Kelvin […]
May 20, 2025
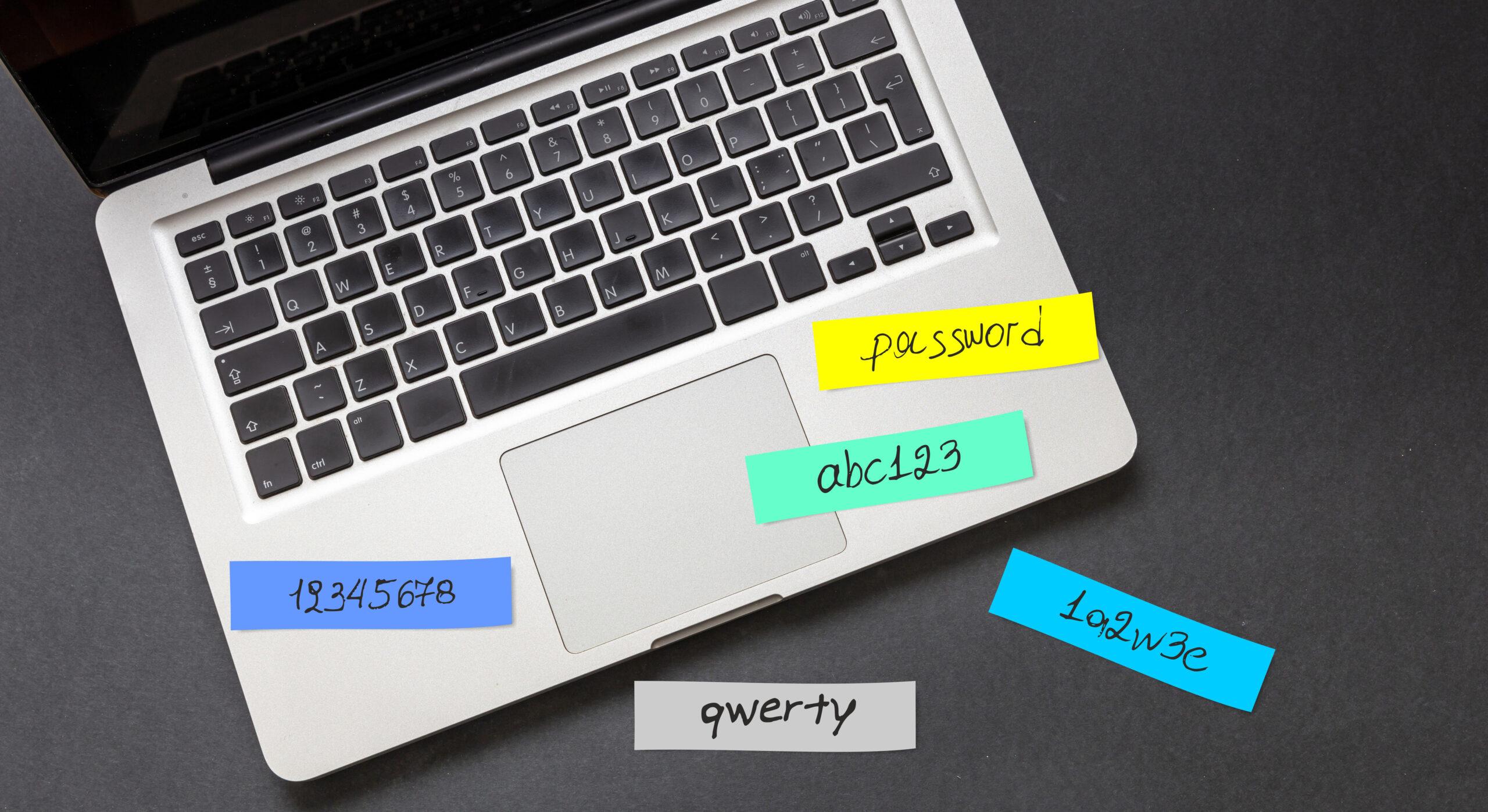
 Businesses rely heavily on their IT infrastructure to stay competitive. A poorly managed IT environment can cause disruptions, security issues, and even loss of productivity. 94% of businesses report that a single hour of downtime can cost them over $100,000. This statistic shows how crucial it is to have the right IT support. Kelvin […]
May 20, 2025
Businesses rely heavily on their IT infrastructure to stay competitive. A poorly managed IT environment can cause disruptions, security issues, and even loss of productivity. 94% of businesses report that a single hour of downtime can cost them over $100,000. This statistic shows how crucial it is to have the right IT support. Kelvin […]
May 20, 2025