Blog / Is There Such A Thing As Too Much Monitoring?
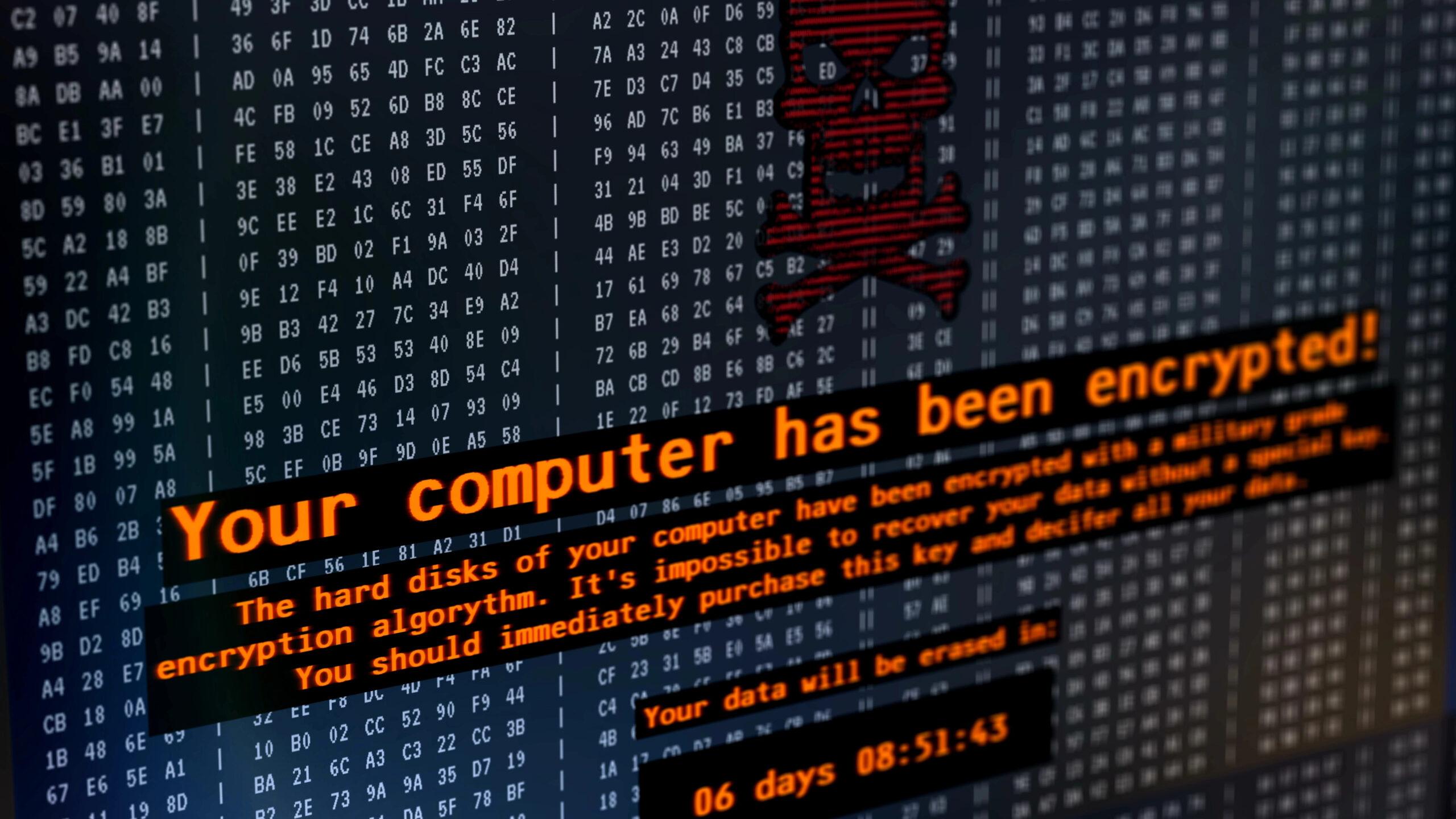
 Effective Monitoring is Efficient Monitoring One of the cornerstones of good cybersecurity is monitoring devices and their activity on your network. After all, you need to keep an eye on what’s happening with your organization’s machines if you hope to detect and defeat threats that have slipped by your defenses, and doing that means monitoring […]
July 23, 2024
Effective Monitoring is Efficient Monitoring One of the cornerstones of good cybersecurity is monitoring devices and their activity on your network. After all, you need to keep an eye on what’s happening with your organization’s machines if you hope to detect and defeat threats that have slipped by your defenses, and doing that means monitoring […]
July 23, 2024
 Effective Monitoring is Efficient Monitoring One of the cornerstones of good cybersecurity is monitoring devices and their activity on your network. After all, you need to keep an eye on what’s happening with your organization’s machines if you hope to detect and defeat threats that have slipped by your defenses, and doing that means monitoring […]
July 23, 2024
Effective Monitoring is Efficient Monitoring One of the cornerstones of good cybersecurity is monitoring devices and their activity on your network. After all, you need to keep an eye on what’s happening with your organization’s machines if you hope to detect and defeat threats that have slipped by your defenses, and doing that means monitoring […]
July 23, 2024