Blog / Decryption as a Service?
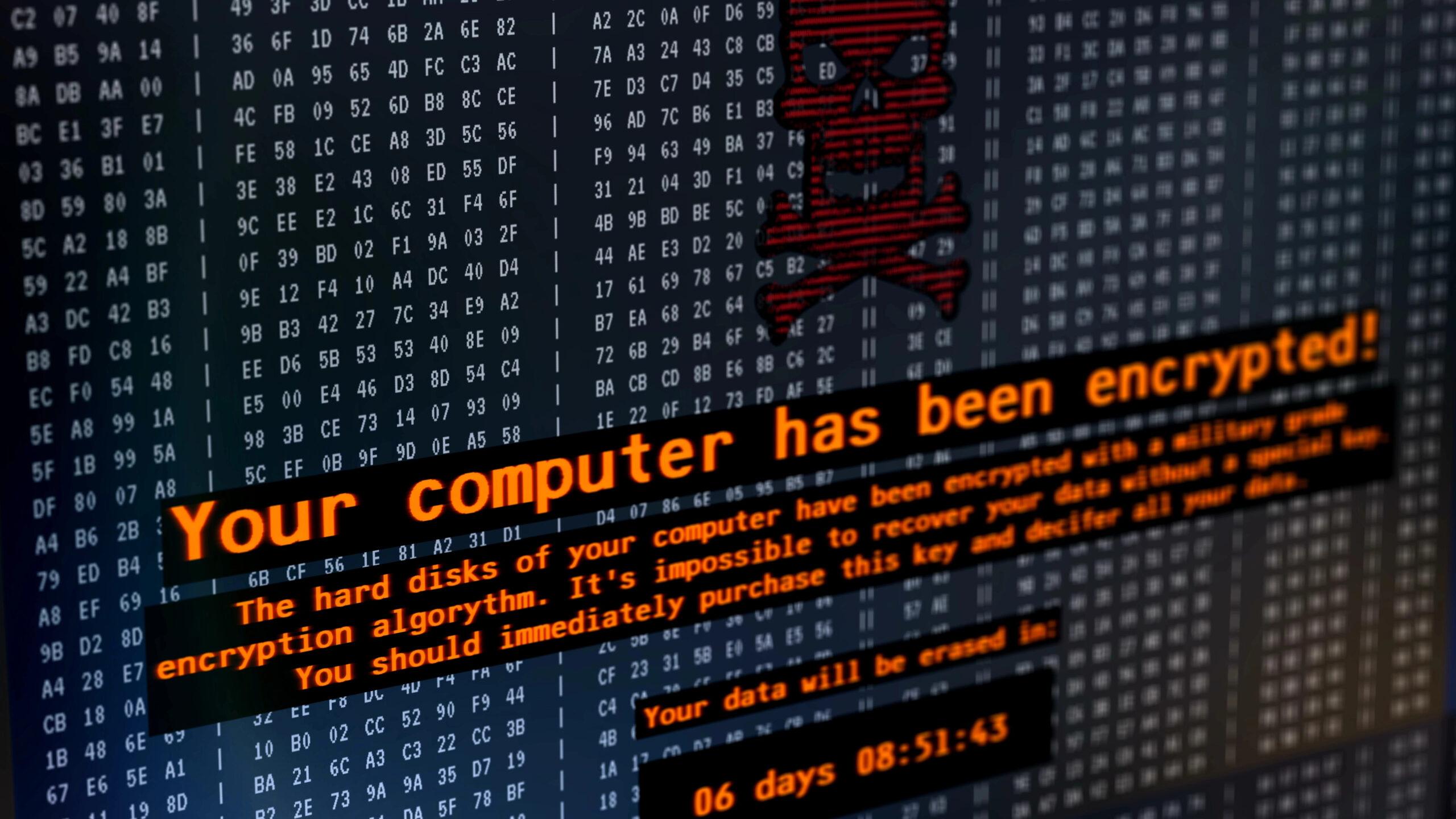 Ransomwares’ latest decryption trick is just one reason to stay up-to-date about cybersecurity. When it comes to security it’s vitally important to ensure your defenses, and the procedures to support them, are actually useful. Any security system that isn’t properly supported and maintained—from physical security like keycard readers on locked doors to cybersecurity tools like […]
July 16, 2024
Ransomwares’ latest decryption trick is just one reason to stay up-to-date about cybersecurity. When it comes to security it’s vitally important to ensure your defenses, and the procedures to support them, are actually useful. Any security system that isn’t properly supported and maintained—from physical security like keycard readers on locked doors to cybersecurity tools like […]
July 16, 2024
 Ransomwares’ latest decryption trick is just one reason to stay up-to-date about cybersecurity. When it comes to security it’s vitally important to ensure your defenses, and the procedures to support them, are actually useful. Any security system that isn’t properly supported and maintained—from physical security like keycard readers on locked doors to cybersecurity tools like […]
July 16, 2024
Ransomwares’ latest decryption trick is just one reason to stay up-to-date about cybersecurity. When it comes to security it’s vitally important to ensure your defenses, and the procedures to support them, are actually useful. Any security system that isn’t properly supported and maintained—from physical security like keycard readers on locked doors to cybersecurity tools like […]
July 16, 2024