Threats Exist in Places Where You Will Least Expect Them … Even Inside Your Own Organization!
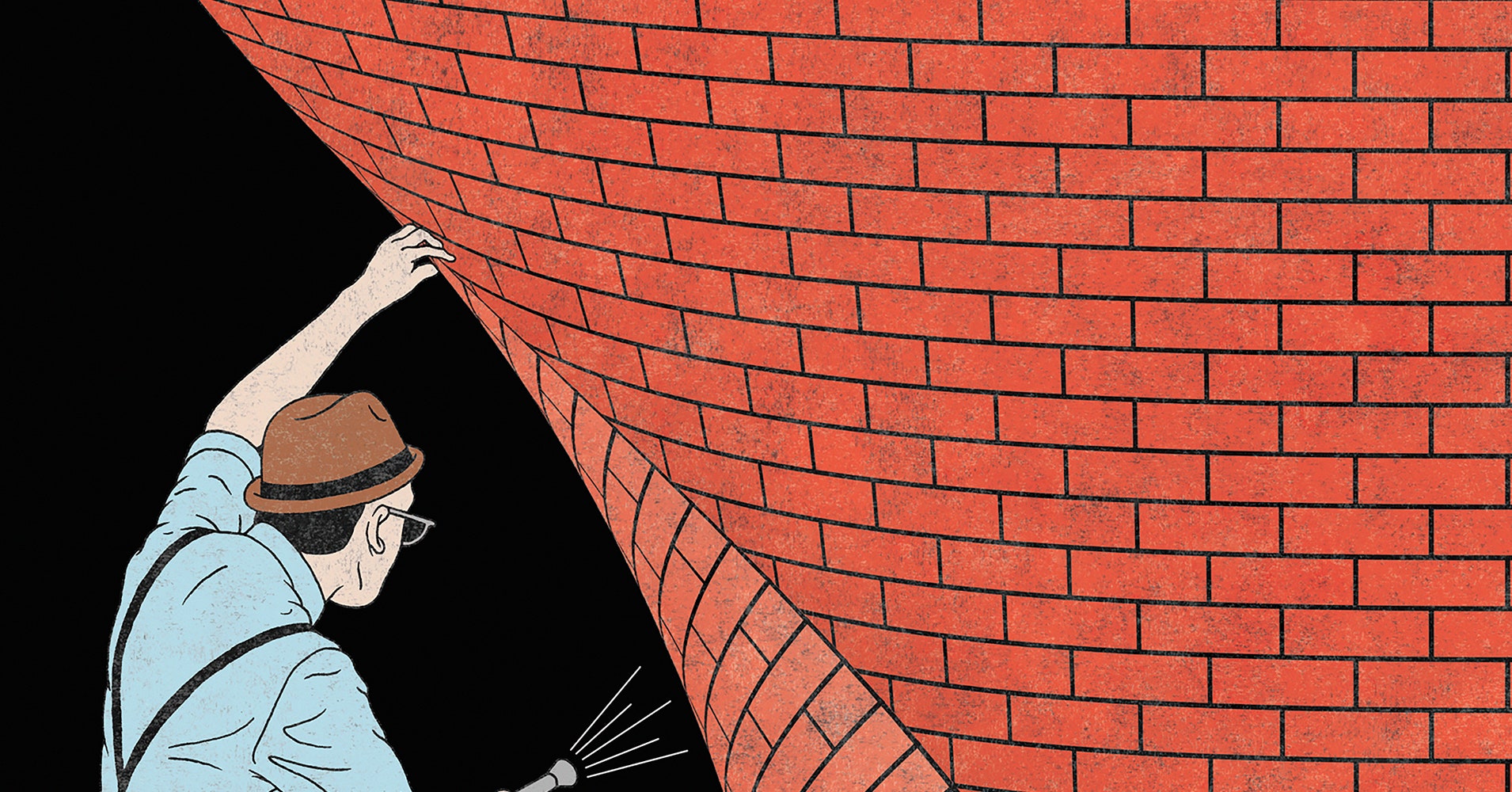
Most organizations will understand dealing with ‘Perimeter Security‘ for their computers. It’s exactly what it sounds like. You put up Security on your network’s perimeter. Anytime your network links with another one (like the Internet), use a Firewall. This is the basic of all basics, even more elementary than installing Anti-Malware software on your computer.
Just because it’s basic doesn’t mean it’s ineffective. Firewalls are very good at keeping an attacker from getting through to the inside of your network. After all, that’s what they were designed to do. So, as an attacker, and knowing that everyone is going to have a firewall, your best chance of success is to find a way to get around the firewall, rather than break through it.
Recently, there was a situation where many high-profile Twitter accounts got compromised, all at the same time. The attackers used the accounts to post false claims, asking people to send bitcoins to a wallet and that twice that many would be then sent back. Sounds corny, but some people fell for it. The last article I read said there was about $130,000 in the attackers’ account. The aggressors were able to change passwords, email addresses and even bypass Two-Factor Authentication. No details about how it happened have been released, as it is still it is being investigated.
The reason I’m bringing this up is because of what the attackers were able to compromise. Being able to change emails and reset passwords, as well as turn off or bypass Two-Factor Authentication, pretty much means that the cyber crooks were able to gain access to some internal management tools. Realistically, this implies either an internal job by a current or ex employee, or a compromised machine. If a machine had been compromised, then the attacker must have known that a strike such as this would have been detected quickly, and they would lose their internal access… so why do it?
Regardless of how it happened, if you consider what was attained, it’s almost certain that internal tools were used to bypass normal checks that get put in place, when you do things the way you’re supposed to. This got me thinking about how typically Network Security is set-up. Most bug guns and money are spent on protecting the perimeter. Very little energy is spent on looking after the insides.
There are 2 important reasons not to forget about the need to protect yourself from internal threats.
1) Employees can abuse their privileges – 2) Employees’ access can be compromised
The more access an employee has, the more their activity needs to be monitored. In terms of computers and networks, this means any and all administrative activity needs to be heavily supervised. It’s not enough just to observe that an admin user logged in; you need to record all kinds of information about how they did so and exactly what they did.
That level of logging is rarely enabled by default and it doesn’t come without a cost. If you are logging that level of activity, then the amount of space your logs take up is going to increase, A LOT. So now you may run into the question of “How far back in time do you want to have logs for?”, because the amount of space this takes up, suddenly makes a big difference when it comes to cost.
I have spent more than two decades doing Technical Support and I’ve seen setups that generated many GigaBytes’ worth of logs, every single day. Doesn’t seem like much, but what if you have a legal requirement to store logs for a year or more (like for PCI-DSS or PIPEDA) and suddenly you need to have several TerraBytes of storage just to keep your logs? That much storage space starts to get costly. Not to mention the fact that you need to also be able to search those logs and if you ever lose them, it’ll be a big problem, so they need to be backed up. You can see where I’m going with this.
Protecting the inside of your network starts with the logs. The job of the Firewall is to keep poachers from getting in. If they get past it, then you need to be able to sort out whatever they did and fix it. Don’t rely on the problem being obvious. First use the logs to find out what happened and then repair it.
I’m not saying you shouldn’t trust your employees. If you can’t rely on them, don’t employ them. All I’m saying is you don’t give out the keys to your kingdom without keeping an eye on them. Logs are a crucial part of protecting your environment. Keep them and monitor them!
If you have any questions about Monitoring Your Logs, please reach out to your TRINUS Account Manager for some stress-free IT.
By Kind Courtesy of Your Friendly Neighbourhood Cyber-Man.

















