Blog / Your Weekends May Never be the Same Again! Most Cyber Attacks Occur on Weekends…
When it comes to Security, I find that doing Thought Experiments are incredibly helpful. A thought experiment is when you try to put yourself into the shoes of someone on the other side of the situation. So, from a Security perspective, thought experiments are when you try to think like an attacker. Put yourself in the shoes of someone trying to get into your corporate network.
Now, it’s important not to assume that anyone trying to do that would be stupid, or obvious. If you do that then the exercise is worthless, because the result of the experiment would be that you catch the perpetrator and your defenses are perfect. Nothing is perfect, so the idea is to find flaws, or potential flaws.
So, let’s take the idea of a physical break-in as a thought experiment. How would you approach the thinking about this?
Well, to start with:
Let us assume the attacker is skilled and has done some appropriate reconnaissance, so they have a good idea of your current Security (alarms, cameras, etc.)
Let us assume they are at least as smart as you are (or smarter), so that they will take the appropriate steps to not get noticed.
Okay, now the situation is ready, and you can start looking around your offices for reasonable ways that a burglar could try and enter the building. But there’s something else to consider:
When is the most likely time for someone to try a break-in?
It’s when the fewest number of people are around. Preferably when nobody is around. So, the most likely time for a break-in to occur would be after the end of the workday, when everyone goes home. This isn’t to say that a break-in wouldn’t happen during normal business hours, just that it’s not as likely.
This is all fine and dandy, but can we use the same sort of thinking when it comes to computers and Network Security? Yes, we can. So, when would a “good time” be for someone to try attacking/hacking your network?
My choice would be the weekend. It just so happens that the article I was reading the other day noted that most attacks actually happen on weekends.
The reasons are pretty obvious:
There won’t be as much traffic on the network, so moving around will be faster.
IT staff will most likely be off or occupied with some kind of activity (maintenance, installations, etc.)
In short, the weekend offers the best chance to slip-in without being noticed.
This can be managed by making sure you have a system in place, that automatically lets your people know there’s something strange going on, and that they need to investigate. Yes, this means that someone is on call 24/7, assuming you want to do this right. To be totally honest, if you aren’t going to do something like this properly, there’s not much point in even considering it.
That’s from a business perspective. From a human perspective, I’ve done that before. I’ve been on-call 24/7 and it SUCKS. From the perspective of having someone do the job properly, it needs to be managed properly. That means an appropriate rotation of responsibility, compensation, etc.
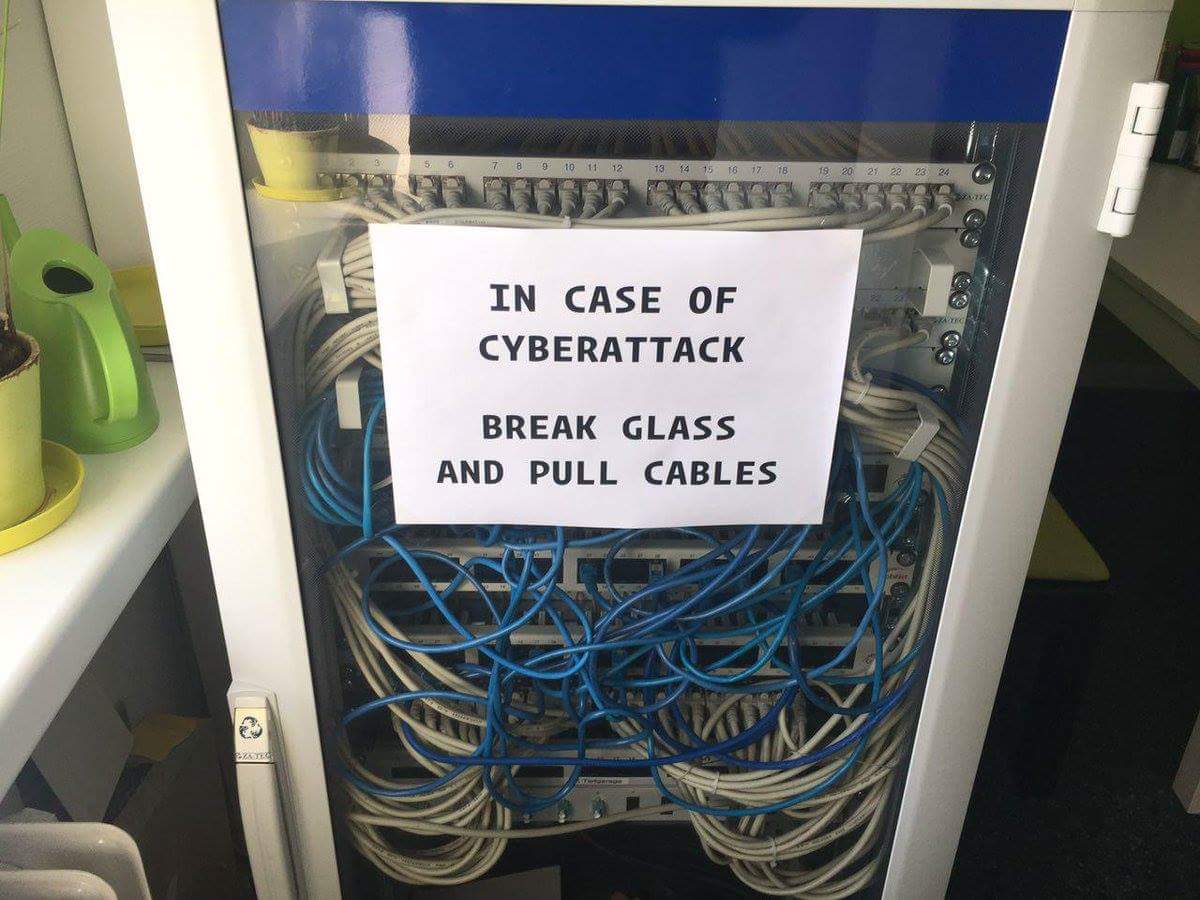
It also means that emergency procedures need to be in place, so that if something big DOES occur after-hours, that useful action can be taken promptly. Detecting an attack at 7 pm and not being able to do anything useful until business hours the next day because a senior manager needs to authorize something, means the after-hours set-up is a complete waste of time.
With all this focus on the electronic aspects, it’s easy to forget that the reason it works in the first place, is because you have people behind it, doing real work. If you just throw this sort of responsibility at someone without any sort of compensation or consideration of emergency measures, you can be certain they will either not put in the effort, or possibly leave.
No one wants to work on weekends, but in order to keep your company cyber-protected, this is an unfortunate reality.
If you have any questions about how to permanently protect your network, you can always reach out to your TRINUS Account Manager for some stress-free IT.

















