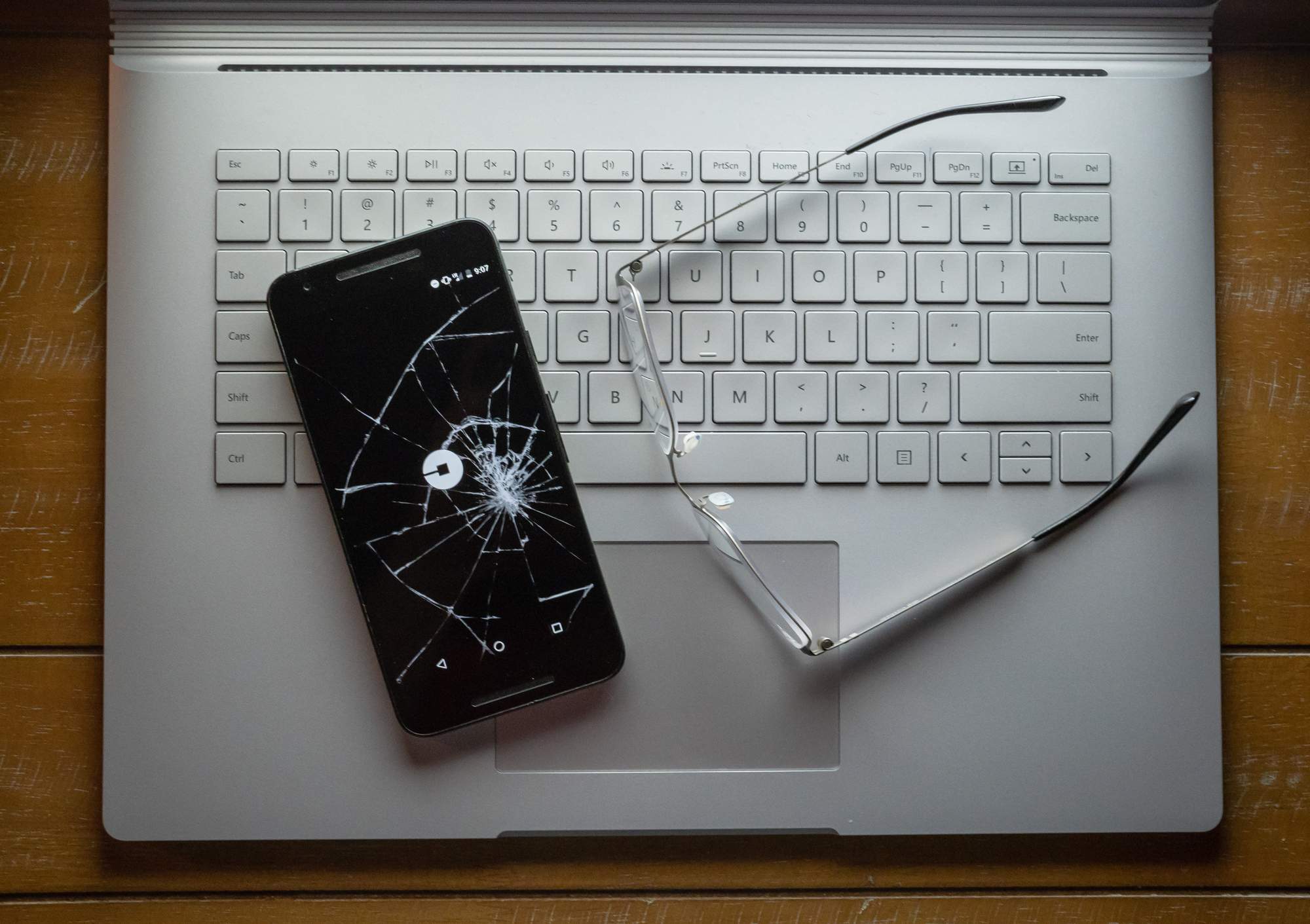
Uber’s Two-factor Failure
Using TFA properly means configuring it right and training personnel.
Did you know Uber was recently hacked? The ride-share and now food delivery giant admitted a contractor’s credentials had been compromised and hackers were able to gain access to sensitive information. Don’t worry yet; although the damage is still being ascertained, the hackers apparently couldn’t get their hands on credit cards numbers and payment information, so don’t go shuttering your Uber account yet.
But how did the hackers get in? Uber’s a tech giant. Surely they have top of the line cybersecurity.
The answer, as usual, is human error. The attackers got ahold of a contractor’s credentials, used them to login, elevated their privileges, then basically ran around Uber’s internal network. The problem is the contractor had setup two-factor authentication, so how could this happen?
Unfortunately, it’s not actually that complicated. Details aren’t given on the specifics of the attack (how fast or slow it was) but clearly rather then attacking and bypassing any of the technology they attacked the person. Uber uses (hopefully “used” by now) a push notification system that asked if the user wanted to allow the login rather then sending a code. Every time the attacker attempted to log in, Uber’s system automatically sent a message to the contractor’s phone. Chances are the attacker timed their login attempt to coincide with when they knew the contractor would be logging in, tricking the contractor into thinking it was a glitch that multiple login requests showed up. Eventually the contractor said yes and just like that the attackers had access to Uber’s network.
That’s how many successful attacks work honestly. In the movies we’re presented with the idea of a hacker being some mad genius frenetically typing away at a keyboard to bypass the firewall and gaining access to the core mainframe and other technobabble. Reality is rarely that exciting. If there’s not a known exploit like Heartbleed involved, the best way to get inside is to attack the people. Phishing attacks are a prime example; they lean heavily on social engineering, psychology, and exploiting peoples lack of knowledge in order to be successful.
This attack on Uber was likely the same. I’ve mentioned before that TFA is not a silver bullet because there’s nothing that can protect you against user error except possibly additional training, and even that won’t be 100%. However, hopefully this incident demonstrates why two-factor authentication shouldn’t be just a push-notification. It’s technically a two-factor system, but hardly as useful as configuring your system to deliver numeric codes or matching challenges like MS Authenticator uses.
Shakespeare’s A Comedy of Errors is where I chose to pluck today’s quote from: “Until I know this sure uncertainty, I’ll entertain the offered fallacy.”
If you’d like help configuring a two-factor authentication system or with training your personnel on the latest cybersecurity standards and best practices, contact one of TRINUS’s cybersecurity experts today and they’ll be happy to help out.
Be kind, courtesy your friendly neighbourhood cyber-man.

















