So, It’s the North Koreans After All!! WannaCry Virus linked to North Korean Hacker
Judging by the popular success of James Bond and Ethan Hunt – and the plethora of Espionage movies, we all like a good spy-action Thriller; especially when it’s coupled with some great action scenes where the Bad Guy gets their comeuppance in a cataclysmic Grand Finale. The Baddie is usually a member of a global organized Crime Syndicate or rogue nation-state. It’s mindless entertainment, but fun nonetheless.
Then we have the media-promoted stereotype of the Cyber Hacker. We are made to believe these individuals are teenagers with bad complexions and questionable personal hygiene, toiling away in their parents’ basements. Their furious typing and mumbling is punctuated with Eureka moments, as another hapless victim falls to their pranks. Of course, they live in an Eastern block country – or one that opposes our Western sensibilities of Justice and Freedom.
Bah, what garbage!
Cyber Criminals are usually highly-educated members of organized crime or nation-states – at least that’s the conventional wisdom. We rarely get a glimpse into the true workings of the Hacker-mill, as few of them are caught – and even fewer ever come to justice.
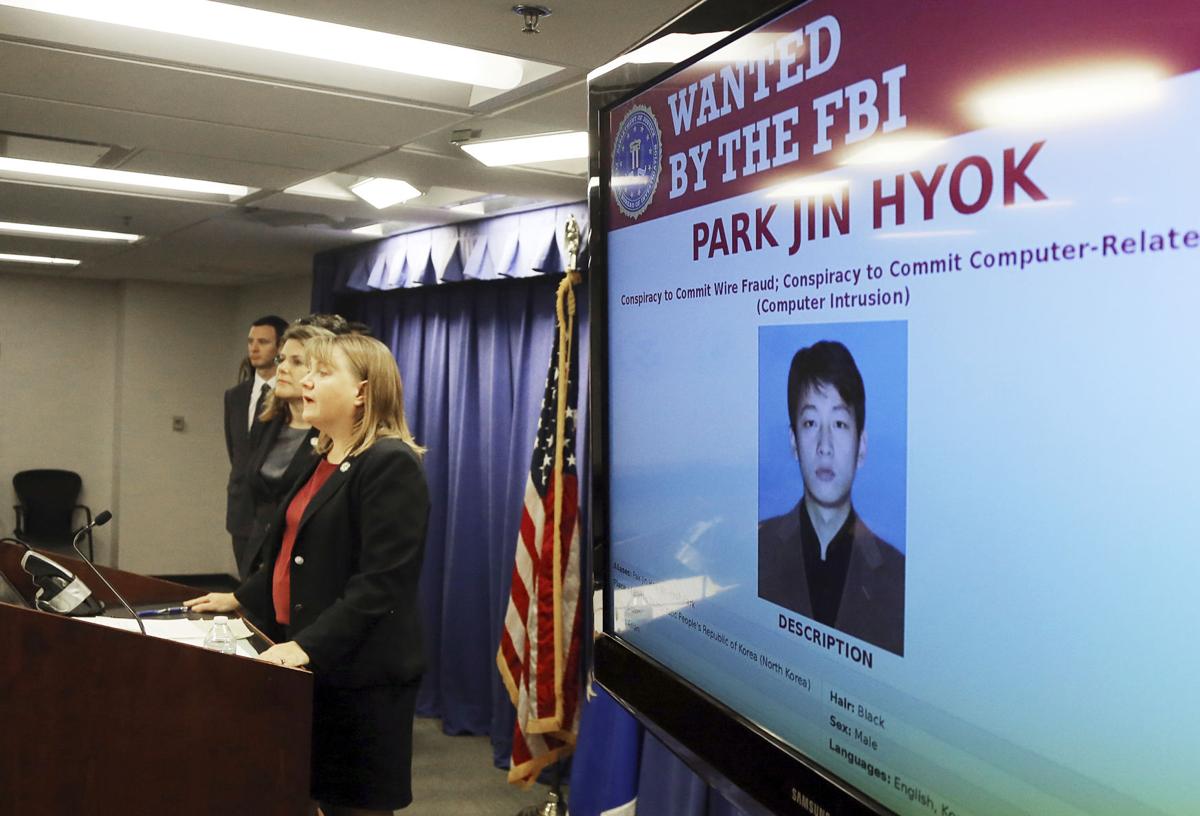
So, last week the FBI announced that Park Jin Hyok – a programmer working for Chosun Expo that operated out of Dalian, China, and is a front for the North Korean government – was responsible for the famous Cyber Crime exploits of the Sony Pictures hack in 2014, the WannaCry virus, and the digital theft of $81 million US from a bank in Bangladesh. Chosun Expo started life in 2002 as an Internet company that employed 20 young graduates from institutions of higher learning in North Korea. Sometime in 2016, the company disappeared from the web, but they appear to be continuing their clandestine operations.
None of this has been proven – and even if it could be, the chances of Park Jin Hyok or any of his colleagues being extradited to the west to face trial, are non-existent.
Apart from an interesting news story, what are the lessons learned? Well, there are three:
Cyber Crime IS nurtured, promoted and encouraged by nation-states and – by inference – Organized Crime. That means perpetrators have sophisticated and extensive resources behind them. It also means the motivation for a particular attack is not always clearly understood. Without understanding the true motive, prevention is harder, as attacks seem random. We can also expect attacks to become ever more sophisticated.
Cyber Crimes are incredibly hard to track to the source. It took the FBI four years to finally identify Park Jim Hyok. But beyond identification, there is little our law enforcement agencies can do to force justice on global perpetrators of Cyber Crime. Besides reporting suspected activity, Users and Organizations are left on their own to formulate a defense.
At the same time, laws are becoming increasingly strict, when it comes to regulating the response from Cyber Crime victims. In Alberta, Municipalities are governed by FOIP, Medical Practitioners by AHS, and every other business and organization by PIPA. Professionals (Accountants and Lawyers, for example) often have their own regulations. All of these force standards of due care and attention when it comes to protecting the Private Information of their Rate-Payers, Patients, Clients, and Staff. They also have strict guidelines when it comes to reporting breaches and mitigating the impact on the people whose information they store.
Of course, that means more cost, more procedures, and more sleepless nights for those in charge.
I am constantly surprised that many organizations are not prepared to treat these attacks and their responsibilities seriously.
We recently had a Medical Practitioner who was attacked by Ransomware – the 3rd time in less than 2 years (Third time’s the Harm.) Their IT infrastructure, Cyber Security Countermeasures, and backups are notoriously inadequate, and so far they have refused to follow even simple recommendations. Each time, it has been a scramble to restore their systems and one of these days, we won’t be able to help; the information will just disappear into Cyber Space.
Or worse, they’ll pay the Ransom! This is bad for many reasons; ask yourself if you really want to become Hacker Park’s Best Repeat Customer.
Unless your name is Ethan or James, and you’re adept at high-speed car chases and advanced Martial Arts, you might want to consider more mundane solutions to fighting Cyber Crime. Anti-Virus, Dynamic Firewall Services and Reliable Backups may seem dull in comparison, but they may help keep you warm and safe at night.
If you would like more information about stress-free Cyber Security, please contact me or your Account Manager for more information.
Thanks!
Dave White
TRINUS
stress-free IT
trinustech.com

















