Municipal IT Budget Planning – Part 4: Municipality Cyber Security
This is part 4 of a 9-part series that will look at selected areas of interest to Municipalities, pertaining to IT Budget Planning. Please contact me if you would like copies of other articles.
Of all the topics we will address in this series, Cyber Security is the newest and least understood. Five years ago, Municipal Cyber Security consisted of Anti-Virus software and a firewall. Cyber Attacks were annoying, but they hardly threatened operations; they might have rendered a few workstations inoperative – or attacked the municipal website, but nothing a few hours of cleanup couldn’t fix.
But now it’s war! If your Municipality hasn’t been hit with Ransomware or some other system-crippling virus, chances are you know of a neighbouring Municipality that has. TRINUS has written almost weekly about the exploits of organized Cyber-Criminals. It’s big business – reportedly estimated at $600 Billion annually, and so is the burgeoning fight against it.
Our focus in this article is to derive a budget for Cyber Security Countermeasures; not to develop a response to Cyber Crime. To avoid confusion, let’s define a few terms:
Cyber Security Assessment: Is a process of evaluating your Municipality’s current state of vulnerability to Cyber Crime, with recommendations to mitigate the risk. Assessments can be one-time, repeated at regular intervals, or have an ongoing vulnerability-scanning component. It’s also important to understand that a Cyber Security Assessment is a snapshot-in-time. Any changes to IT systems or threats can drastically change the Assessment’s Requirements and Recommendations. The most important Recommendations are the ones that address systemic problems that need corrections.
Cyber Security Countermeasures: Are your activities that reduce your risk to Cyber Attacks. Anti-Virus, dynamic firewall filtering, password rule enforcement, and User Policies and Education, are a few examples of these activities.
Backups and Disaster Recovery: Discussed in Part 2 of this series, this is your response-process for System Recovery, in the event a Cyber Attack renders your IT systems unusable. Often forgot, Cyber Insurance can be a critical part of a Cyber Crime Disaster Recovery effort – as it can provide funding to recover from a Cyber Attack, including funds to mitigate the cost of Legislative Reporting and Recovery Requirements, Public Notifications, and Technical Support.
The state-of-the-art for fighting Cyber Crime is in it’s infancy. While most Municipalities have some rudimentary Countermeasures in place, few have opted for an Assessment, and fewer still have Cyber Crime Response baked into their Disaster Recovery Program. The need for Cyber Crime-fighting efforts will increase in the next 12 to 24 months, as Legislative Requirements and the need for public due-diligence increase. This will have a major impact on Budgeting.
While Budget-Planning for a Cyber Security Assessment is straight-forward (based on standard formulas and the size of your operations), planning to act on the Report Recommendations could add significant costs to the budget. Thus, we are going to increase our Budget Contingency to 20% AND add an arbitrary Capital Cost Allowance, based on the assumption that you’re going to have to fix something – you just don’t know what yet.
Finally, while previous articles provided options for Budget Planning, Cyber Security really just has 1 option: either you do it properly or you don’t. Here’s our scenario *:
- New System – or one that’s LESS THAN 5 years old (Little Idea #2 **)
- No Cyber Security Assessment has been done in the past 18 months
- IT Systems comprised of:
- 1 x Physical server hosting 4 Virtual (VM) servers
- (Domain Controller, File Server, Exchange Email & Applications)
- 4 Network Devices (Firewall, Switch & 2 x Wi-Fi Access Points)
- 25 Workstations & Laptops
- 1 x Physical server hosting 4 Virtual (VM) servers
- 3 Locations – Main Office, Public Works and Firehall
- 35 Users or User Accounts
- Budget Plan: 12 months
Notice that 2 more parameters have been added to our scenario; locations and TOTAL number of Users. Cyber Security Assessments inspect some physical aspects of Security (i.e.: access to servers and critical network equipment, Backup Media Security, etc.) – and the number of IT system Users and Accounts may be greater than the number of Municipal-owned workstations and laptops. For example, elected Officials or part-time and Volunteer Staff may have Email accounts or limited system access through personal devices (Smartphones) or a shared computer.
Capital Costs
- Implement Cyber Security Assessment recommendations: $5,000
- (Contingent on Cyber Security Assessment)
- Sub-total: $5,000
Operating Costs:
- Annual Cyber Security Assessment: $3,500
- (25 Users + 3 Locations)
- Cyber Security Countermeasures:
- 30 x Anti-Virus (A/V) Licenses: $120 x 12 = $1,440
- (Monthly Subscription – 25 Workstation/Laptops + 1 Hosting Server + 4 x VM Servers)
- 1 x Dynamic Firewall Subscription: $125 x 12 = $1,500
- (Monthly Subscription for Advanced Firewall Blocking)
- 1 x Email Server SPAM Filtering: $50 x 12 = $600
- (Monthly Subscription for Email SPAM and A/V Pre-filtering)
- 5 x Two-Factor Authentication Services: $60 x 12 = $720
- (Monthly Subscription for 5 x Secure VPN Server remote accounts)
- 35 x User & File Access Monitoring and Reporting: $140 x 12: $1,680
- (Monthly Subscription for 35 User accounts)
- 30 x Anti-Virus (A/V) Licenses: $120 x 12 = $1,440
- Cyber Insurance Premiums: $500 ***
- Sub-total: $9,940
- Total: $14,940
Total Budget: $14,940 + 20% contingency = $17,928 -> $18,000
This is a significant cost that – for the most part – was not part of the IT System Budget 5 years ago, and like Backup and Disaster Recovery expenses, there are no perceived performance, reliability, or usability enhancements for the end-User. It appears to be just a straight cost, and so the insurance-mindset is required when planning for Cyber Security.
Apart from possible enhancements as part of the Cyber Security Assessment report, the Operational Budget is just maintaining status-quo for most Municipalities. A/V licenses, Firewall subscriptions, and Email pre-filtering, should already be part of your Cyber Security Countermeasures. It’s equally likely that enhanced measures will be required in the near future. Example: Real-time vulnerability scanning (the ability to monitor existing – and new – devices, and evaluate their Cyber Security Risk) will be coming to a network near you.
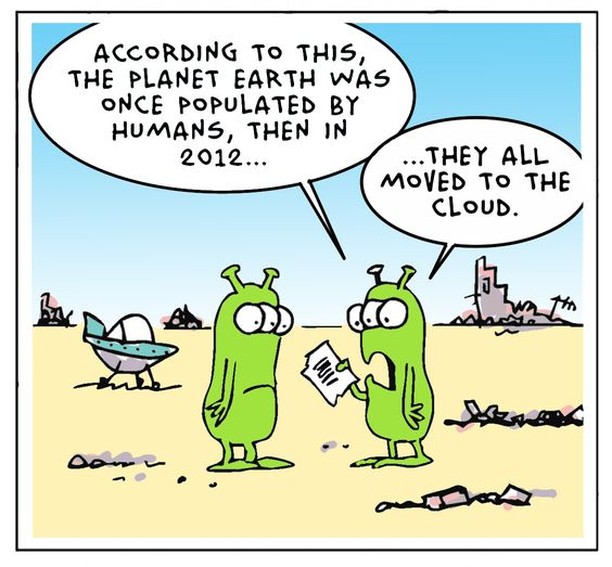
Finally, there is a complicating factor that has not entered the equation; the move towards Cloud-based Services for Municipal functions. As systems and functions are moved offsite to Cloud Providers – be they Private or Public – the need to evaluate THEIR Cyber Security readiness becomes an important part of your overall Cyber Security planning. Just because it’s Google or Amazon, don’t assume their Cyber Security arrangements meet your requirements – especially around international data storage and access. Evaluating a large Provider can be a difficult (and expensive) process – and this might be an advantage to the new class of Boutique (Private) Cloud Suppliers that are emerging. For example, TRINUS is making a significant investment in our Private-Cloud Data Centre, to host systems for Alberta Municipalities that meet their specific Cyber Security needs.
Next week, we’ll explore Servers. Until then, please contact me or your Account Manager, if you would like some personalized help with some stress-free Cyber Security Budgeting.
Thanks!
Dave White
TRINUS
stress-free IT
trinustech.com
* – Full Disclosure: We’re going to use Services and prices for TRINUS-supplied Systems and Services. Other Provider costs and equipment may vary.
** – Little Ideas – along with the BIG IDEA – were presented and defined in Part 1 of this series
*** – Placeholder-estimate ONLY for Cyber Security Insurance

















