The Internet of Things
Ah… the Internet of Things, or IoT for short. There are many things you can talk to Cyber-Security professionals about that will make their blood pressure rise, and this is one of them.
What is IoT?
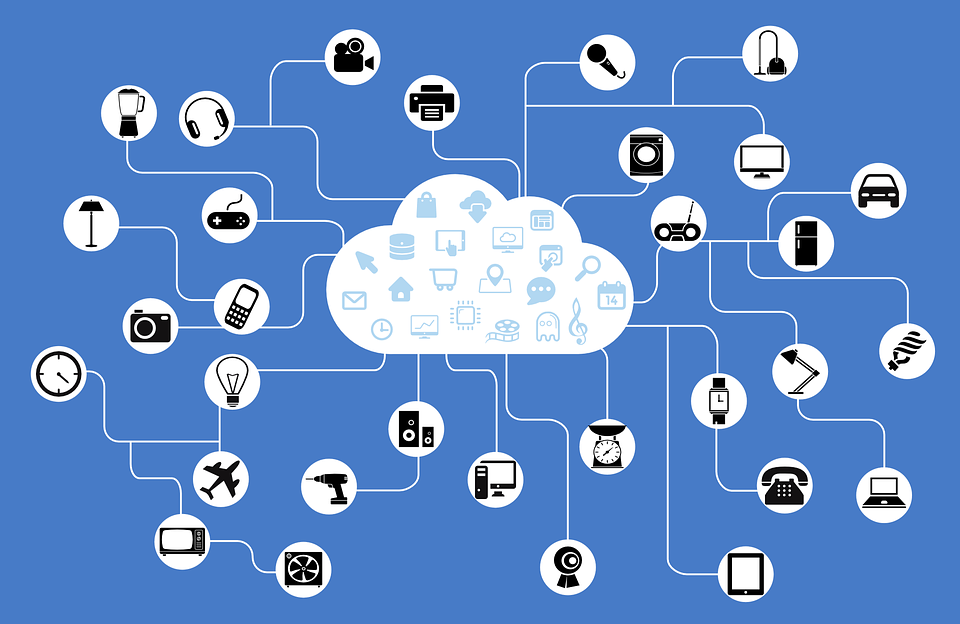
IoT stands for the Internet of Things. Now most people are used to having computers and firewalls and their network. IoT devices are all those other network-aware devices. They include things like cameras, fridges, light switches, light bulbs, and just about anything you can imagine that can be connected to a network.
Why does IoT make your head hurt?
Well, it’s not the fact that someone decided to make a fridge that could access the Internet. I’m a geek at heart, so I’m all for blinking lights and tech.
The problem is purely one of Security. Many of these IoT devices are not regulated in any way. This means that manufacturers don’t need to follow any sort of standards or testing practices to make sure their products are secure. There are some devices with hard-coded administrative login credentials with no way of being removed. Other devices have interfaces that are so poorly coded, they can be easily bypassed and reprogrammed.
Well if there’s a bug, they can just patch it.
Not necessarily. In order to keep costs down, only the bare minimum of hardware is generally installed on these sorts of devices. This means that if a vulnerability is found, it may be impossible to fix it, because the software would become too big.
So as a computer guy, how do you deal with IoT devices?
Pretty simply, honestly. Anything that I can’t run Antimalware on (either by a direct install or through remote-scanning), I lock up in a separate part of my network. This includes things like printers (even network printers: they can’t have Antimalware run on them). If it’s a device I need to access or manage (like a network printer), I ensure that communications to it are available, but locked down (only the ports necessary to use and administer it are open). I want to ensure that the only thing it gets used for is what it was intended to be used for. This keeps my critical infrastructure devices (computers, servers, etc.) safe from being attacked by a compromised IoT device. If you think that IoT devices are safe because they are small and not very powerful, then you haven’t heard of the Hajime botnet (300k+ IoT devices).
If there are IoT devices that need to access the Internet, I try to ensure that they pass through a firewall with Antivirus and Intrusion protection-enabled and scanning all the traffic. While this is no guarantee, it’s better than nothing. If they do not need to access the Internet, I make sure that the network design (firewall policies and routing) do not allow them to, if they tried.
Maybe in the future, more legislation/regulations will get put in place to force these companies to make better products. Right now, it’s a gamble on which devices have undergone rigorous design-testing and which ones have not. As anyone who gambles will tell you, the best way to win is to try and tip the odds in your favour. The way you win at Security is Smart Design. So, design your networks with the reality of IoT in mind and may the odds be ever in your favour!
If you ever wonder about your Electronic Security or have any questions about IoT, you can always reach out to your TRINUS Account Manager for some stress-free IT.
Your Friendly Neighbourhood Cyberman.

















