Blog / Network Segregation – by Your Friendly Neighbourhood Cyberman
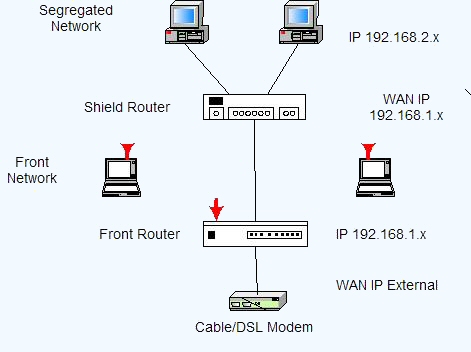
| Something that gets thrown around IT circles a bit is the concept of “Network Segregation.” From a Security standpoint, this idea is great; however from an administrative perspective, it does make the design of things more complicated. The overall idea is that rather than having a single “Company Network” that all devices have access to, you create multiple separate networks and limit the amount of access between them. In a previous Newsletter I talked about locking up your IoT devices in a separate part of your network: https://www.trinustech.com/the-internet-of-things/
Today I’d like to take this idea a step further. Every company needs to consider the types of network devices that they are responsible for. These can include (but are not limited to): HVACs Network Printers Desktop Computers Portable Computers (Laptops/Tablets) Servers Smart Phones Industrial Control equipment Cameras Debit machines Card strikers etc.
The following is an idealistic list of different networks that could exist within a company. How many your company should use will depend on the types of devices and network equipment you have.
Location Infrastructure Your first network should be comprised of all the devices that are required for that location’s operation. This includes things like HVAC units, Card Strikers, Cameras, etc. Essentially group together the devices that are needed to keep that location open and secure. Generally, this network will be totally wired, but there’s no reason it could not also include a wireless portion.
Company Network This network could be a combination of a wired and wireless setup. It includes all the user devices that are permanently kept in that location. It would include servers, desktops, and possibly some laptops or tablets (if they are intended to remain on premises.)
Portable Device Network This network is one that would be used by the portable devices that belong to the company (No personal devices!) It could include smart phones and other portable devices that are routinely removed from the location, so long as they are the property of your company. This would be a completely wireless network. If your company has multiple locations, having a standard setup for this network could make moving between locations seamless for employees and their devices. These devices should be kept separated, simply because if they are taken off-site, they become a Security risk.
BYOD/Guest Network This would be a wireless network that employees could connect their personal devices to while at work. Employees should NEVER connect their personal devices to a network designed for internal (company-owned/managed) devices. Some companies may combine their BYOD and Guest networks into one, others might set them up as separate networks. It would depend on if there were going to be different rules for use and access restrictions.
IoT network This would be the network intended to be used by all those IoT devices (a catch-all network). Smart light switches, IP enable light bulbs, etc. Depending on the nature of the IoT devices, some of them could be a part of the Infrastructure network. Not every company needs to have all these networks, but most should have at least 2 or 3. The benefits of a setup like this when you have multiple locations, is that your network setup can be standardized. This makes transitioning equipment from one location to another, easy. It also makes the job of your IT team easier, as each location has similar network setups.
Communication between networks Now that all your devices are separated based on their purpose/function/owner within your company, you can improve the Security even more, by addressing the question of what traffic to allow to travel between each network. For example: Does the IoT network need to access the company network? Probably not; however, the company network may need to be able to access some devices in the IoT network, to do proper monitoring. Does the BYOD network need to access the building infrastructure network? No.
Communications between devices in your network This is something that often gets overlooked. Some devices within your network may be managed by 3rd party Contractors. Setting up outside access to those devices is one thing. However, something that is often overlooked is the potential access they can obtain within your network when they access those machines. For example, let’ s say your phone system is Cloud-based and managed by a 3rd party company. If such outfit is able to connect to those phones remotely, can they access other devices that aren’t phones? If they can, then so could an attacker. You may be required to lock up or separate devices within the same network, in order to properly secure your environment. Once you can identify and define the valid routes for communication, your network devices (switches, firewalls, subnets, etc.) can be configured to enforce this behaviour. This will have the effect of compartmentalizing your network-capable devices and limiting what an attacker could potentially access.
If you’re looking for help with separating devices within your own network, you can always reach out to your TRINUS Account Manager for some stress-free IT.
Thank you! Your Friendly Neighbourhood Cyberman. |

















